Phishing: How to Recognize and Avoid Social Engineering Attacks
The Complexity of Phishing and Social Engineering
In today’s digital landscape, phishing attacks have evolved to become both more sophisticated and widespread, posing significant threats to individuals and organizations alike. Cybercriminals harness a variety of deceptive techniques to trick unsuspecting users into divulging highly sensitive information, such as passwords, credit card numbers, and personal identification details. Therefore, it is crucial for everyone, from casual internet users to corporate employees, to develop skills that help them recognize and combat these insidious threats.
Phishing extends beyond the misleading emails that first come to mind. It encompasses a wider range of tactics under the umbrella of social engineering, a psychological manipulation method used to exploit human emotions and behaviors. Here are some of the most common forms of phishing you should be wary of:
- Email Phishing: This involves deceptive emails that masquerade as genuine communication, often imitating trusted entities such as banks or popular online services. For instance, a user might receive an email claiming there has been unusual activity on their bank account, prompting them to click on a link that directs them to a fraudulent website.
- Spear Phishing: Unlike generic phishing attempts, spear phishing is targeted communication aimed at specific individuals or organizations, often utilizing personal information to create a compelling reason for the recipient to engage with the attacker. For example, cybercriminals may reference a recent event or shared connection with the victim, making the attacker seem more credible.
- Smishing: In this digital age, phishing is not limited to email; it also occurs via SMS messages. A smishing attack might involve a text message that appears to be from a service provider, prompting the user to click a malicious link to resolve an urgent issue.
- Vishing: Voice phishing involves phone calls where attackers impersonate legitimate organizations to extract sensitive personal information. This could involve a caller claiming to be from a well-known company, requesting verification of account details under the guise of customer support.
Understanding these tactics is the first step toward safeguarding your personal and financial information. A significant aspect of successfully identifying phishing attempts is comprehending the underlying motivations of these cybercriminals: often, they seek financial gain, identity theft, or to gain access to valuable corporate resources.
In the following sections, we will delve into effective strategies for recognizing and avoiding phishing attempts. By mastering the ability to spot the signs of deceit, you empower yourself and others in your community, thereby creating a safer environment in our increasingly interconnected world. Awareness is an invaluable tool—one that can be the difference between personal security and potential financial disaster.
DON’T MISS: Click here for essential tips to save on cloud storage costs

Identifying the Red Flags of Phishing
The prevention of phishing attacks begins with recognizing the red flags that are often woven into the fabric of fraudulent communications. As phishers continuously refine their tactics, being able to spot these warning signs is essential for protecting your personal and financial information. Here are several notable indicators that can help you differentiate between legitimate messages and potential phishing attempts:
- Unusual Requests: Legitimate organizations rarely ask for sensitive information via email or text messages. Be particularly cautious if a message requests prompt action, such as verifying account details, transferring money, or clicking on a link to download files.
- Misspellings and Poor Grammar: Phishing messages often contain typographical errors and awkward phrasing. Although some attackers invest time into crafting professional-looking messages, many do not, making frequent mistakes a hallmark of phishing attempts.
- Urgency and Fear Tactics: Phishing scams frequently invoke a sense of urgency to manipulate the recipient’s reaction. Messages may claim that your account will be suspended or that immediate action is required to safeguard your information. This strategy preys on emotions and compels victims to act quickly without careful consideration.
- Suspicious Links or Attachments: Always hover over links before clicking to see the actual URL they lead to. Many phishing messages will direct you to fake websites that appear legitimate at first glance. Additionally, unexpected attachments can harbor malware; therefore, it’s prudent to avoid opening any unsolicited files.
- Generic Greetings: Pay attention to the salutation used. Messages that begin with general terms such as “Dear Customer” can be suspect, as genuine communications will often use your name or personal details.
By staying alert to these warning signs, users can significantly reduce their risk of falling victim to phishing threats. However, awareness alone is not enough. Education plays a pivotal role in enhancing one’s defenses against these attacks. It is vital to understand that phishing is a constantly evolving threat, requiring individuals to remain updated with the latest phishing tactics and techniques.
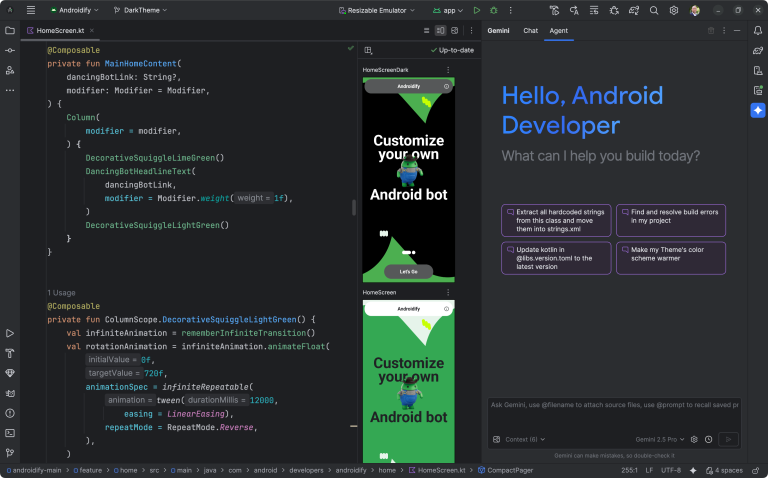
Moreover, organizations should consider implementing regular training sessions for their employees. This not only raises awareness but also fosters a culture of caution and vigilance within the corporate environment. Many businesses are already employing multifactor authentication and email filtering systems to mitigate risks associated with phishing, but personal vigilance remains an indispensable layer of security.
Ultimately, recognizing the tricks used by cybercriminals is the first line of defense in the ongoing battle against phishing. Becoming proficient in identifying the nuances of social engineering will empower users to safeguard themselves in the digital realm effectively.
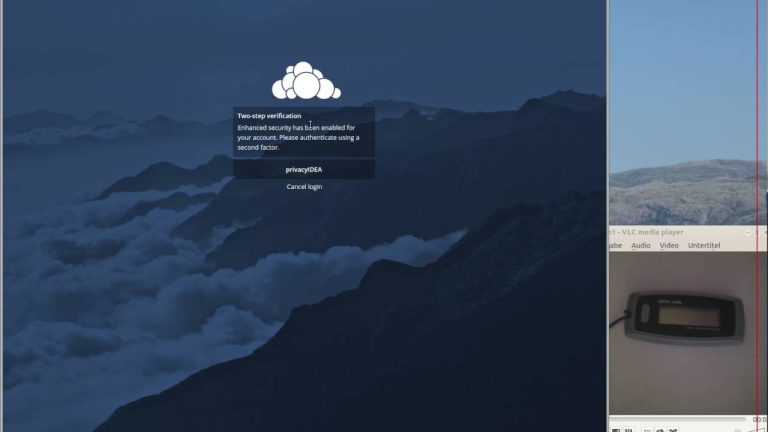
Phishing attacks are a growing concern as cybercriminals continue to develop more sophisticated methods to deceive users. Recognizing these threats is crucial in protecting personal information and maintaining cybersecurity. An essential step in this process is to be aware of the different types of phishing attacks. Email phishing is one of the most common forms where attackers masquerade as legitimate entities to trick users into providing sensitive data. Always analyze the sender’s email address, hover over links to reveal URLs, and look for signs of urgency or threats in the message. These tactics are designed to manipulate emotions, making individuals act impulsively. Social engineering plays a significant role here, as attackers exploit psychological triggers. Educate yourself on the common strategies used in phishing scams, such as pretexting, where attackers create a fabricated scenario to obtain information. By understanding these tactics, you can better defend against potential threats.Educating friends and family about recognizing phishing attacks is also vital. Conducting training sessions on cybersecurity awareness can significantly reduce the risks associated with social engineering. Share resources that provide examples of phishing emails and websites to ensure everyone knows what to avoid. Additionally, employing security measures such as two-factor authentication lends an extra layer of protection. This makes it significantly more challenging for attackers to access your accounts even if login credentials are compromised. Incorporating these practices not only aids in personal security but also fosters a safer online environment for everyone. As awareness grows, phishing tactics will need to evolve, highlighting the importance of understanding these attacks to remain one step ahead. Always remain vigilant, and don’t hesitate to report suspicious activities to the relevant authorities.
DON’T MISS: Click here to discover cost-saving strategies
Protecting Yourself Against Phishing Attacks
While recognizing the red flags of phishing is crucial, protecting yourself against these social engineering attacks involves a layered defense strategy. Being proactive in your online habits significantly reduces the risks associated with phishing and helps in safeguarding sensitive information. Here are some essential practices to help you stay ahead of cybercriminals:
- Utilize Strong Passwords: Employ unique passwords for different accounts and consider using a password manager to keep track of them. Strong passwords should include a mix of uppercase letters, lowercase letters, numbers, and special characters. Regularly changing passwords, particularly after a suspicious email or breach, is also vital.
- Enable Multifactor Authentication: Whenever possible, enable multifactor authentication (MFA). This adds another layer of security; even if a phisher manages to obtain your password, the additional step required to access your account will deter them.
- Educate Yourself and Others: Staying informed about the latest phishing techniques is essential. Subscribe to security newsletters and attend cybersecurity training sessions. Encourage family and colleagues to do the same—awareness is a collective tool against phishing.
- Verify Unusual Activity: If you receive communications regarding unusual activity on your accounts, independently verify the claim by contacting the organization directly. Use official contact methods found on the organization’s legitimate website rather than the contact information provided in the suspicious message.
- Be Cautious with Public Wi-Fi: Using unsecured public Wi-Fi networks can increase vulnerability to phishing attempts. Avoid accessing sensitive information or conducting transactions over public networks. If necessary, consider using a virtual private network (VPN) to encrypt your online activities.
Moreover, being mindful of your digital footprint can also play a role in defending against phishing. Social media platforms can be goldmines for phishers, who often study personal information to craft convincing messages. Limit the amount of personal information shared online, and review your privacy settings regularly to ensure that you are not inadvertently providing attackers the ammunition they need to target you.
The Role of Technology in Phishing Prevention
Technological solutions also augment your defenses against phishing attacks. More businesses are employing advanced email filtering systems that identify and block potential phishing attempts before they reach users’ inboxes. These systems can analyze email headers, detect suspicious links, and flag messages with known indicators of phishing.
Additionally, consider using security solutions that provide real-time protection against phishing attempts. Some browsers now include built-in protection features that warn users of potentially dangerous sites or alert them to unsafe downloads.
Moreover, keeping software and operating systems updated is paramount. Many updates include security patches designed to close loopholes that phishers may exploit. Regularly updating your devices ensures you have the latest security features, which fortify your defenses against online threats.
As phishing techniques continue to evolve, so must our strategies for dealing with them. By adopting a multi-faceted approach that combines awareness, education, and technological defenses, you can significantly lower the risk of becoming a victim of these manipulative attacks.
DISCOVER MORE: Click here for expert tips
Conclusion: Staying One Step Ahead of Phishing
As our reliance on digital communication continues to grow, so too does the threat of phishing and social engineering attacks. Understanding how to recognize these malicious tactics is imperative for every internet user. By being vigilant and informed, you can spot the warning signs and significantly diminish the chances of falling victim to these deceitful schemes.
Ultimately, a proactive approach—combining strong passwords, multifactor authentication, and regular education on the latest phishing trends—will equip you with the necessary tools to defend against cyber threats. It is equally important to verify unusual account activity through trusted channels and remain cautious when using public Wi-Fi networks. By sharing this knowledge with friends, family, and coworkers, you create a network of vigilance that benefits everyone.
The technological landscape also plays a crucial role in our defense. As enhanced email filtering systems and browser protections continue to advance, leveraging these tools can provide an added layer of security against potential phishing attempts. Moreover, keeping your software up to date ensures that you are fortified against the latest vulnerabilities.
In conclusion, while phishing tactics are becoming increasingly sophisticated, so too are our means of countering them. By adopting a multifaceted approach that encompasses awareness, education, and technology, you can stay one step ahead of cybercriminals, protecting not only yourself but your sensitive information. The fight against phishing is an ongoing endeavor, and together, we can enhance our collective cybersecurity resilience.
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.