Two-Factor Authentication: Enhancing the Security of Your Accounts
The Importance of Two-Factor Authentication in Today’s Digital World
As our digital lives continue to expand, the number of threats targeting our sensitive information has escalated dramatically. This evolving landscape of cyber threats requires individuals and businesses to adopt more robust security measures to safeguard their online presence. One of the most crucial advancements in account security is the implementation of two-factor authentication (2FA), which has emerged as a vital safeguard against unauthorized access.
How Two-Factor Authentication Works
Two-factor authentication operates on the principle that gaining access to an account should involve more than just a password. When 2FA is enabled, users must provide two distinct forms of verification. This typically consists of something they know (their password) and something they have or are (a verification code or biometric identifier). This additional step provides a significant barrier for cybercriminals, even if they manage to acquire the user’s password.
The forms of 2FA vary, enhancing user experience while maintaining high security standards. Common methods include:
- Authentication apps: Applications like Google Authenticator or Authy generate time-sensitive codes that users enter during the login process.
- Text messages or phone calls: Users receive a unique code via SMS or a phone call, which they must input to gain access.
- Biometric data: Features such as fingerprints or facial recognition provide a seamless yet secure experience, often built into smartphones and laptops.
Why You Should Implement Two-Factor Authentication
The necessity for 2FA is underscored by alarming statistics; a recent study unveiled that over 90% of data breaches could have been mitigated through the use of two-factor authentication. This statistic highlights a critical point: while passwords are often the first line of defense, they are frequently inadequate against sophisticated hacking tactics.
For example, consider a scenario where a user’s email password has been compromised through a phishing scam. Without 2FA in place, a hacker could easily access sensitive accounts linked to that email. However, with two-factor authentication enabled, even with the password, the attacker would be unable to log in without also having access to the secondary verification method.
Getting Started with Two-Factor Authentication
Setting up two-factor authentication is typically straightforward and can be done through the security settings of most online services. Users are encouraged to enable 2FA on crucial accounts, especially those that manage sensitive data, like financial services or personal correspondence. Moreover, many platforms now prompt users to activate this feature during the account creation process, emphasizing its significance in enhancing security.
In conclusion, understanding and implementing two-factor authentication is not just advisable—it has become essential for anyone aiming to protect their digital identity. Whether you’re safeguarding personal emails, securing social media profiles, or managing sensitive information for a business, 2FA is a critical step towards maintaining your online security in an increasingly perilous digital landscape.
DON’T MISS: Click here for essential tips
Understanding the Mechanisms Behind Two-Factor Authentication
Two-factor authentication (2FA) provides an essential layer of security by ensuring that users must validate their identity through more than just a password. The idea is simple but effective: by requiring two distinct elements from the user, the potential for unauthorized access is greatly diminished. Let’s delve deeper into the mechanisms behind this important security feature and examine how it operates in practice.
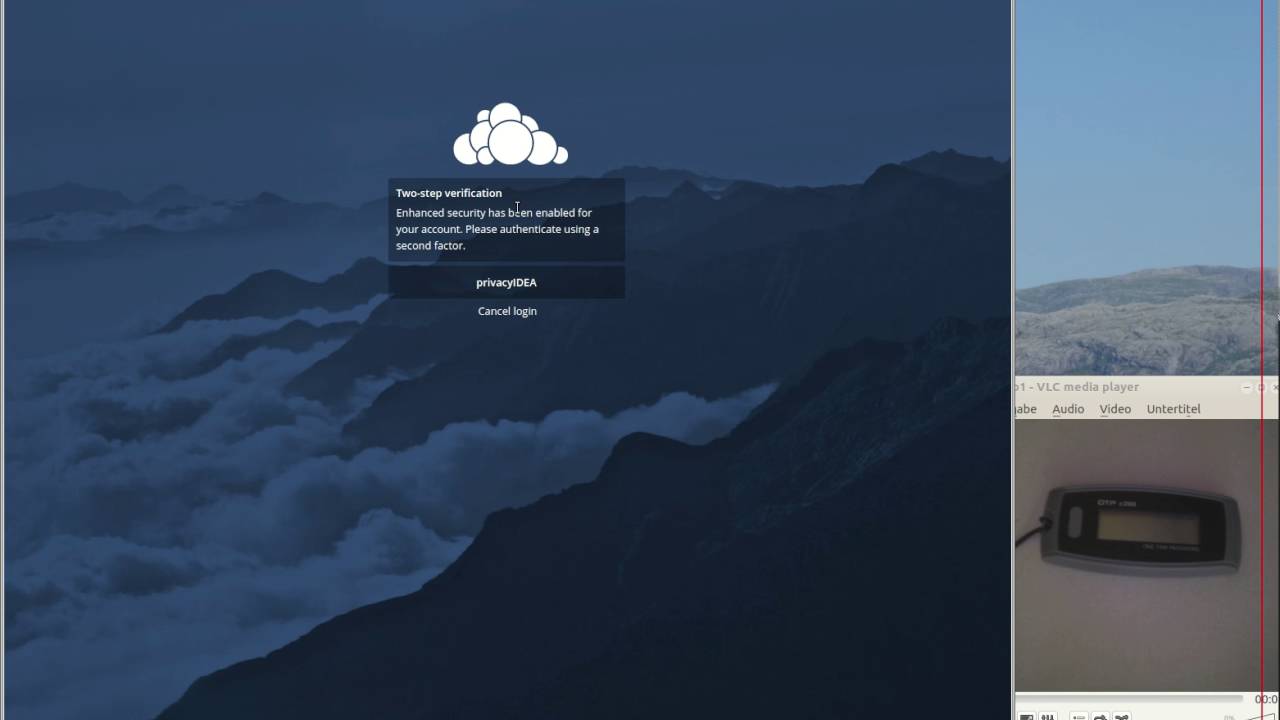
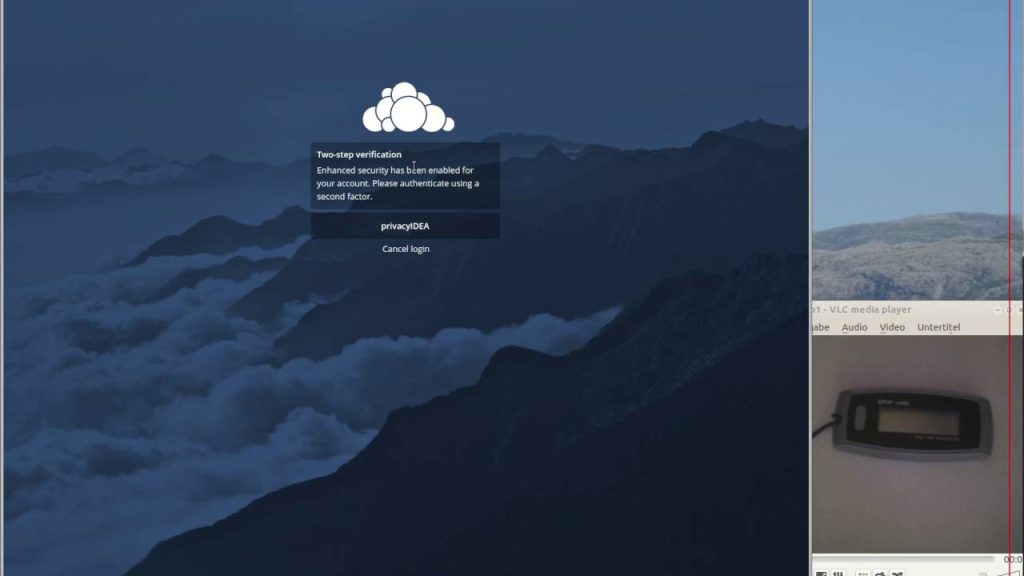
Initially, when a user attempts to log into their account, they are prompted to enter their password as usual, which constitutes the first factor of authentication. Once the password is validated, the system will trigger the second step, which requires a secondary piece of information. This second factor can take several forms, each designed to add another layer of complexity for anyone trying to bypass security protocols.
Common Methods of Two-Factor Authentication
As previously mentioned, the forms of 2FA can vary widely, catering to different user preferences and security needs. Here are some of the most common methods:
- Authentication apps: Many users rely on apps like Google Authenticator or Microsoft Authenticator, which generate a unique time-sensitive code. This code changes every 30 seconds, making it incredibly difficult for an attacker to use even if they somehow gain access to the first factor (the password).
- SMS and Voice Calls: Receiving a verification code via text message or phone call is another popular method. While convenient, it’s worth noting that this method can be vulnerable to SIM swapping attacks. Cybercriminals may deceive a telecommunications provider to gain access to your phone number temporarily, potentially compromising your accounts.
- Biometric Verification: Many devices today come equipped with biometric technology such as fingerprint scanners and facial recognition. This method not only enhances security but also offers a user-friendly experience, as it can often be completed with just a touch or glance.
Each method comes with its own advantages and disadvantages, but the overall goal remains the same: to significantly reduce the risk of account compromise. Users are encouraged to assess which methods work best for them, taking into consideration their lifestyle, the risks they face, and the sensitivity of the information they are protecting.
The Growing Relevance of Two-Factor Authentication
The increasing relevance of two-factor authentication is bolstered by rising cyber threats. According to the 2022 Verizon Data Breach Investigations Report, a staggering 81% of hacking-related breaches involved stolen or weak passwords. This highlights the critical need for additional security measures like 2FA. In a world where personal and financial data can be exploited in seconds, the adoption of two-factor authentication is not just a proactive defense mechanism; it is quickly becoming a standard practice.
Moreover, the demand for Two-Factor Authentication has seen an increase in recent years as businesses prioritize safeguarding customer information. Major service providers, including Google, Facebook, and banks, now actively promote the availability of 2FA as part of their security offerings. The message is unmistakable: in today’s digital landscape, taking these extra steps to secure your online accounts is essential.
In summary, understanding the mechanisms of two-factor authentication is critical for users aiming to fortify their online security. The proactive measures individuals take today will significantly impact their ability to protect personal information from cyber threats tomorrow.
Understanding Two-Factor Authentication
Two-Factor Authentication (2FA) is a crucial layer of security designed to protect your accounts against unauthorized access. By requiring two forms of verification before granting access, 2FA significantly reduces the risk of security breaches. The common process combines something you know, like a password, with something you have, such as a temporary code sent to your mobile device.
How Does Two-Factor Authentication Work?
The essence of Two-Factor Authentication lies in its dual verification process. When attempting to log into an account, users first enter their username and password. Once this initial step is completed, a second verification is triggered. This could be a code generated by an authentication app, a text message, or even biometric data like fingerprint recognition.
| Advantages | Importance |
|---|---|
| Improved Security | 2FA minimizes the chance of unauthorized access to your accounts, thus bolstering personal and financial security. |
| Enhanced Account Protection | By adding an extra layer of verification, sensitive information is less likely to be compromised, providing peace of mind for users. |
By understanding and implementing Two-Factor Authentication, users take significant steps toward safeguarding their personal data and boosting their overall cybersecurity posture. As cyber threats continue to evolve, the importance of adopting such security measures cannot be overstated. Explore the various options available for enabling 2FA, and stay a step ahead in the quest for account security.
DISCOVER MORE: Click here for valuable insights
The Importance of Choosing the Right Two-Factor Authentication Method
While two-factor authentication (2FA) significantly boosts the security of online accounts, it is essential for users to evaluate and select the most appropriate method for their needs. Not all 2FA methods provide the same level of protection, and understanding these differences can help individuals safeguard their sensitive information better.
Evaluating Security Levels
When choosing a method for two-factor authentication, consider the security levels each option provides. Authentication apps, while not completely foolproof, have proven to be more secure than SMS-based verification. According to a study by the National Institute of Standards and Technology (NIST), using authentication apps can dramatically lower the chances of being compromised compared to methods relying on text messages. The fundamental reason lies in the way each method functions; the codes generated by apps are stored locally and require no network connection, making them far less susceptible to interception.
Accessibility and Usability
While security is of paramount importance, usability also plays a critical role in the adoption of two-factor authentication. Users are more likely to engage with security measures if they are not cumbersome or overly complicated. Biometric verification systems, like fingerprint or facial recognition, are lauded for their ease of use. According to a Frost & Sullivan report, over 75% of consumers prefer biometric authentication methods for their convenience. However, users must ensure that their devices support such features and that appropriate data privacy measures are in place to protect biometric information.
The Future of Two-Factor Authentication
As cyber threats continue to evolve, so too will two-factor authentication technologies. Experts predict that the future may hold advancements such as adaptive authentication, which evaluates user behavior and context to determine the appropriate level of security for each login attempt. For example, if you regularly log into an account from the same device and location, the system might require only a password. Alternatively, if you try to log in from a new device or location, additional verification steps will ensue.
Organizations are also beginning to adopt methods that incorporate machine learning and artificial intelligence. These technologies can mitigate risks in real-time by assessing login behaviors and recognizing anomalies that may indicate a security breach. According to research by Gartner, more than 60% of organizations plan to enhance their identity verification processes with AI by 2024, indicating a clear shift toward more intelligent authentication systems.
Incorporating Two-Factor Authentication into Daily Life
Implementing two-factor authentication isn’t just for tech-savvy individuals or large organizations; it can be easily integrated into everyday life. Many popular services, such as online banking and social media platforms, offer 2FA as a default setting. Users must take the initiative to enable these features during account setup or in their account settings.
Furthermore, creating awareness about the importance of 2FA amongst friends and family can promote better cyber hygiene within your community. The more people who understand and utilize 2FA, the stronger the collective defenses will be against cyber threats.
Ultimately, as the digital world continues to expand, so does the necessity of employing measures such as two-factor authentication. The choices users make today in adopting robust security measures for their online accounts will resonate through their future online experiences, underscoring the critical nature of this vital protection.
DISCOVER MORE: Click here for tips on optimizing cloud storage and reducing costs
Conclusion: The Imperative of Two-Factor Authentication
In an age where online threats are more sophisticated than ever, two-factor authentication (2FA) emerges as a crucial line of defense for digital security. By requiring an additional layer of verification beyond the traditional password, 2FA markedly reduces the risk of unauthorized access to sensitive information. As discussed, selecting the right method of two-factor authentication is paramount; from the relative security of authentication apps compared to SMS codes to the user-friendly nature of biometric systems, making informed choices is essential for effective protection.
Moreover, as technology progresses, so too will the innovations in two-factor authentication. The future promises advancements like adaptive authentication and AI-driven verification methods that will enhance security measures even further. Embracing these technologies can empower individuals and organizations to stay one step ahead of potential threats, protecting not only personal data but also fostering a safer online ecosystem.
Understanding the importance of integrating 2FA into daily internet usage can serve as a critical step towards safeguarding personal and financial information. As consumers, we must take initiative, not just for ourselves but also in promoting this security practice within our communities. The ripple effect of widespread adoption can significantly bolster collective defenses against cyber assaults. Ultimately, enhancing the security of our accounts requires a proactive approach; implementing two-factor authentication today lays the groundwork for tomorrow’s peace of mind amidst a rapidly evolving digital landscape.
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.