Cloud Security: How to Protect Your Data Stored Online
Understanding the Importance of Cloud Security
As businesses continue to embrace cloud computing at an unprecedented rate, they are increasingly vulnerable to various security threats. The shift to online platforms means that data, which once resided primarily on in-house servers, is now stored in cloud environments, making it essential to grasp the intricacies of cloud security. As companies look for flexibility, scalability, and cost-efficiency, the potential risks such as data breaches, unauthorized access, and data loss grow significantly.
The escalation of cyber threats is particularly concerning. Recent reports indicate that cyberattacks targeting cloud services have seen a sharp uptick, with statistics showing a notable rise in ransomware attacks—a method where attackers encrypt critical data and demand a ransom for its release. Moreover, with sensitive customer information housed in the cloud, the impact of a security incident can be severe, resulting in not only immediate financial losses but also long-lasting damage to a company’s reputation.
In addition to the heightened risk landscape, the necessity for compliance with data privacy regulations cannot be overlooked. Laws such as the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the United States establish strict guidelines for the handling and protection of personal data. Failing to meet these regulations can result in hefty fines and legal repercussions, further underscoring the importance of robust cloud security measures.
A security breach can have a far-reaching impact on business operations. For instance, a well-publicized incident at a major retailer not only led to millions of dollars in recovery costs but also resulted in a significant decline in customer trust, which affected sales for years afterwards. Customers increasingly value transparency and security, making it imperative for businesses to prioritize their cloud security strategies.
Implementing Effective Cloud Security Measures
To protect valuable data in the cloud, organizations should consider employing multiple security practices. One of the most effective methods is encryption. This process involves converting information into a code to prevent unauthorized access. It is crucial to ensure that data is encrypted both in transit (when moving between devices) and at rest (when stored in the cloud). This dual-layered approach significantly enhances the security of sensitive information.

Another critical aspect is the establishment of access controls. By implementing strict user access protocols, organizations can limit the number of employees who can view or manipulate sensitive data. Role-based access control (RBAC) is an effective approach whereby employees are granted access only to the information necessary for their job functions, thereby minimizing potential exposure.
Finally, organizations should prioritize regular audits of their cloud security systems. Conducting routine security assessments helps identify vulnerabilities that may have gone unnoticed. Identifying and addressing these weaknesses can prevent potential breaches before they occur.
As the digital landscape continues to evolve, the necessity for meticulous cloud security measures becomes increasingly apparent. Understanding and implementing effective strategies not only protects sensitive data but also secures customer trust, paving the way for sustainable business growth in an increasingly connected world.
DON’T MISS OUT: Click here to discover cost-saving tips
Implementing Robust Cloud Security Practices
As organizations increasingly rely on cloud storage for managing vast amounts of data, prioritizing cloud security has never been more crucial. With various cloud service models available—such as Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS)—each presents distinct vulnerabilities that could be exploited by cybercriminals. To safeguard sensitive information stored online, businesses must adopt a comprehensive approach encompassing the following practices.
- Data Encryption: A cornerstone of effective cloud security, encryption transforms sensitive information into an unreadable format unless decrypted with an appropriate key. Organizations should implement encryption for data in transit and at rest. For added security, consider adopting advanced encryption standards, such as AES-256, to protect against unauthorized access during transfer and while stored in the cloud.
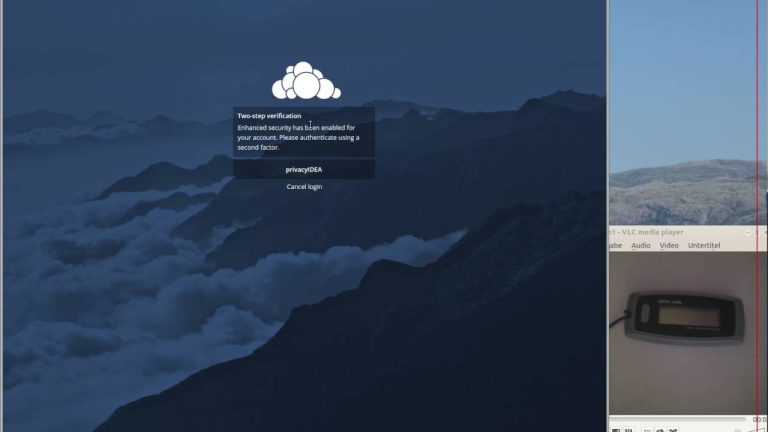
- Multi-Factor Authentication (MFA): Enhancing access security is vital in minimizing unauthorized entry. MFA requires users to provide multiple forms of verification—such as a password and a unique code sent to their mobile device—before granting access to sensitive data. This additional layer of security significantly decreases the likelihood of breaches stemming from stolen passwords.
- Regular Security Audits: Continuous evaluation of your cloud infrastructure is essential for identifying potential vulnerabilities and assessing compliance with industry standards. Conducting routine security audits helps uncover weaknesses that may not be readily apparent, allowing organizations to address them proactively.
- Data Backup Solutions: Implementing a robust data backup strategy is crucial for protecting against data loss due to accidental deletion, hardware failures, or cyberattacks such as ransomware. Regularly backing up data in multiple locations—ensuring backups are cloud-based and offline—provides a safety net for organizations, allowing for swift recovery when needed.
- Access Management: Establishing a solid access control system is critical to minimizing the risk of unauthorized data exposure. Employing role-based access control (RBAC) ensures that employees have only the necessary access to perform their roles, limiting the potential for insider threats and accidental data breaches.
With the increasing volume of confidential information being stored in the cloud, organizations must take proactive steps to secure their data. In addition to the aforementioned strategies, staying updated on emerging threats and industry best practices can help businesses stay one step ahead of potential attackers. This dynamic approach not only protects valuable data but also instills confidence among customers, further reinforcing the organization’s commitment to safeguarding their information.
Moreover, the implementation of a strong security culture within the organization cannot be underestimated. By fostering an environment where employees understand the importance of cloud security and are trained to recognize potential threats, businesses greatly enhance their defense mechanisms. Ultimately, by combining sophisticated technology with informed personnel, businesses can create a fortress that guards against the complex and evolving challenges of cloud security.
| Advantage | Description |
|---|---|
| Data Encryption | Encrypting your data adds a layer of protection, ensuring that unauthorized users cannot access your sensitive information. |
| Scalability and Flexibility | Cloud security solutions allow businesses to easily scale their resources as needed, adapting to changing security requirements. |
In the rapidly evolving landscape of digital threats, leveraging cloud security measures becomes essential. Organizations are recognizing the importance of employing advanced data encryption techniques, which convert readable data into an encoded form. This process not only mitigates the risk of data breaches but also enhances compliance with regulations such as GDPR.Furthermore, the inherent scalability of cloud solutions allows businesses to adjust their security infrastructure seamlessly. As their data storage needs grow or shrink, companies can adapt without overcommitting resources or falling behind in security capabilities. This flexibility fosters a more resilient approach to data protection.Each of these advantages contributes significantly to the overarching goal of safeguarding sensitive information. By prioritizing cloud security, individuals and organizations can protect their digital assets from the myriad threats present in today’s interconnected world.
DIVE DEEPER: Click here for essential tips
Leveraging Advanced Technologies for Enhanced Security
As organizations seek to strengthen their cloud security measures, the integration of advanced technologies becomes essential for not only safeguarding data but also optimizing overall security posture. The ongoing evolution of threats necessitates businesses to look beyond conventional methods. Below are key technologies and practices that can bolster cloud security.
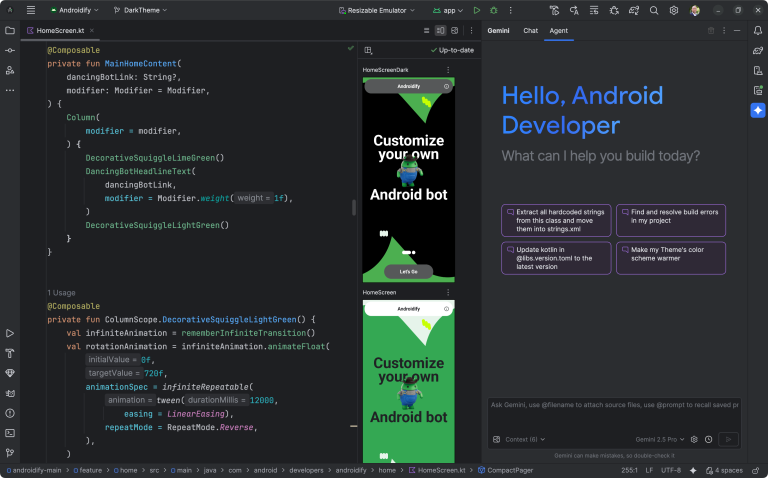
- Artificial Intelligence (AI) and Machine Learning (ML): Organizations can harness the power of AI and ML to identify potential security breaches before they escalate. By analyzing user behavior patterns, these technologies can flag unusual activities that deviate from established norms, prompting timely alerts. For instance, if an employee’s account suddenly attempts to access data volumes significantly higher than usual or from unfamiliar locations, AI can help spot this anomaly rapidly, enabling swift remediation.
- Cloud Security Posture Management (CSPM): Implementing CSPM solutions allows organizations to have a continuous assessment of their cloud configurations. These tools automatically identify risks and compliance violations by using automation to enforce best practices. With serious breaches often arising from misconfigured settings, CSPM enhances the organization’s ability to maintain a secure cloud environment.
- Zero Trust Architecture: Embracing a zero trust model mandates that verification is required from everyone trying to access resources within the network. This principle assumes that threats could exist both outside and within the organization, establishing a culture of least privilege access. With zero trust, organizations can increase data protection by ensuring continuous authentication and authorization checks, even within the corporate network.
- Threat Intelligence Services: Engaging with threat intelligence services provides organizations with up-to-date insights into emerging risks and evolving threat landscapes. These services analyze vast amounts of data to identify trends and potential attacks. Staying informed allows businesses to prepare more effectively for possible incidents, adapting their security strategies based on current threats.
- Compliance Automation: Regulatory frameworks such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA) impose strict guidelines on data protection. Utilizing compliance automation tools aids organizations in adhering to these regulations effortlessly. Automating compliance processes reduces the chances of human error, ensuring consistent monitoring and reporting of compliance status.
Another vital aspect of cloud security is the management of third-party services. As companies frequently work with external vendors for various services, it’s imperative to conduct thorough due diligence. Organizations should assess the security measures implemented by these partners, ensuring that they align with their own security standards. A comprehensive third-party risk management program can minimize the risk of vulnerabilities posed by vendors that may compromise sensitive data.
Furthermore, integrating security information and event management (SIEM) systems allows organizations to collect, analyze, and respond to security incidents in real-time. With effective SIEM tools, businesses can centralize their security monitoring, streamlining their response efforts and facilitating quicker investigation of potential incidents. By implementing these advanced systems, organizations can not only enhance their security strategies but also act proactively to deter threats.
By employing these advanced strategies, organizations can fortify their defenses against the myriad of threats they face in today’s digital landscape. As cloud environments continue to evolve, adapting these cutting-edge technologies ensures robust protection, remaining resilient in an ever-changing threat landscape.
LEARN MORE: Click here for expert tips on optimizing cloud storage
Conclusion: Fortifying Your Digital Assets in the Cloud
In the age of digital transformation, the importance of cloud security cannot be overstated. As organizations increasingly rely on cloud storage solutions to manage and protect sensitive data, understanding how to secure this information is paramount. The multifaceted approach to cloud security—coupled with a solid grasp of advanced technologies—equips businesses to combat evolving threats effectively.
By leveraging tools such as artificial intelligence, cloud security posture management, and zero trust architectures, companies are better positioned to anticipate and thwart security breaches. These technologies not only enhance the security posture but also promote a proactive strategy in risk management. Additionally, integrating threat intelligence services and compliance automation enables organizations to remain vigilant and compliant with regulatory requirements, reducing exposure to potential legal repercussions.
Moreover, the role of third-party risk management cannot be overlooked. As businesses collaborate with various vendors, ensuring that their security measures align with your organization’s standards is essential in safeguarding against vulnerabilities. A robust supply chain security strategy contributes significantly to overall cloud security health.
In conclusion, companies must prioritize their cloud security measures as they navigate the complexities of the digital landscape. By continuously adapting their strategies, investing in advanced security technologies, and fostering a culture of security awareness, organizations can significantly enhance their resilience against cyber threats. Embracing this proactive stance is not just a best practice; it is a necessity in today’s interconnected world. As you explore further, consider the specific implications of these technologies for your organization’s security framework, and prepare accordingly for the challenges and opportunities that lie ahead.
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.