Emerging Trends in Data Security for Cloud Solutions in 2024
Emerging Trends in Data Security for 2024
As businesses increasingly migrate to cloud solutions, the importance of robust data security measures has never been more critical. Cybersecurity threats are evolving at an alarming rate, making it essential for organizations to stay ahead of the curve. With the rapid evolution of technology, 2024 is poised to introduce several game-changing trends in data security that organizations must not overlook. Understanding these trends and their implications could mean the difference between thwarting a cyberattack and facing severe data breaches.
Here are some notable developments to watch for:
- Zero Trust Architecture: This strategy operates on a “never trust, always verify” principle, a marked shift from traditional cybersecurity models that assume trust within internal networks. In practice, this means that every access attempt—whether from an employee or an external entity—is scrutinized. For example, companies like Google have successfully adopted Zero Trust by continually validating user identities and devices, ensuring that only authenticated users can access critical data.
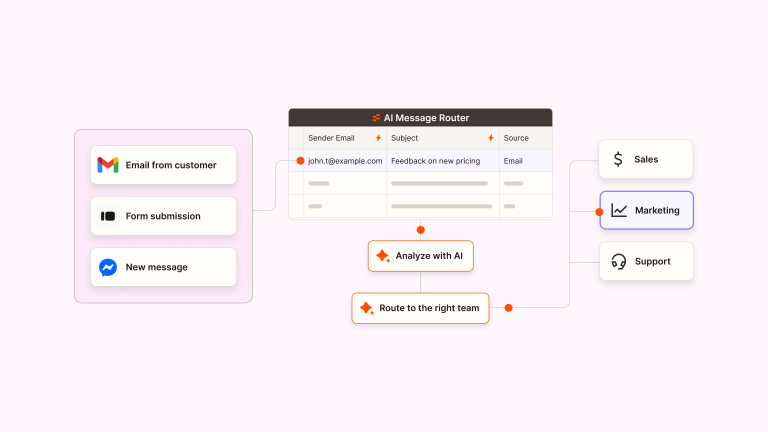
- AI-Driven Security: The integration of artificial intelligence in cybersecurity is revolutionizing threat detection and response methodologies. Machine learning algorithms can analyze large amounts of data to identify abnormal patterns that may indicate a cyber threat. Companies like Darktrace are already harnessing AI to create autonomous response systems that can react to threats in real time, significantly reducing response times and potential damage.
- Decentralized Identity Solutions: The traditional methods of user authentication are being challenged by the rise of blockchain technologies. Decentralized identity solutions allow users to control their data without relying on centralized servers, enhancing privacy and security. For instance, projects like Sovrin are developing frameworks that empower users with self-sovereign identities, minimizing the risk of identity theft—a frequent concern for organizations handling sensitive customer information.
- Data Encryption Enhancements: As data breaches become more common, improving encryption methods for data both at rest and in transit is vital. Advanced encryption techniques, such as homomorphic encryption, allow data to be processed while still encrypted. This means sensitive information remains secure even during analysis, promoting confidentiality without sacrificing usability. Companies investing in such technologies will be at the forefront of protecting their clients’ data.
These trends reflect a growing need for organizations to safeguard sensitive information against increasingly sophisticated cyber threats. With the rise of remote work and digital transformation driven by the global pandemic, adopting a proactive stance has become essential to mitigate risks. A recent survey indicated that nearly 80% of IT leaders in the United States believe that workplace transformations will lead to increased vulnerabilities, underscoring the urgency for enhanced security measures.
By staying informed and adapting to these trends, businesses can ensure their cloud solutions remain secure and resilient. As we explore these emerging trends in detail, it is crucial to recognize their potential to shape the future landscape of data security in 2024 and beyond. Join us as we delve deeper into these developments, examining their implications and the strategies that organizations can employ to protect their assets effectively.
Dive Deeper: Click here to learn how to optimize your cloud storage and cut costs!

Zero Trust and the Shift in Cybersecurity Paradigms
The concept of Zero Trust Architecture is garnering significant attention as organizations strive to fortify their defenses against increasingly sophisticated cyber threats in 2024. Unlike traditional security frameworks, which often operate on the assumption that internal users and devices are inherently trustworthy, Zero Trust mandates a rigorous verification process for every access request. This approach mitigates the risk of unauthorized access, as each user must prove their identity each time they wish to access sensitive data or systems.
According to the latest industry research, more than 70% of U.S. organizations are expected to adopt Zero Trust models within the next year. Such noteworthy adoption highlights the level of urgency companies feel to enhance their cybersecurity posture amid escalating data breaches. Organizations like Microsoft and Google have also embraced this model, demonstrating its effectiveness in reducing vulnerabilities. By continuously assessing user permissions and device security, businesses can prevent lateral movement within their networks, making it increasingly difficult for cybercriminals to exploit exposed assets.
AI-Driven Security: The Future of Threat Detection
Another emerging trend enhancing data security within cloud environments is the integration of artificial intelligence (AI) into security protocols. As cyber threats continue to evolve, traditional methods of threat detection are proving inadequate. AI-enhanced systems, capable of analyzing vast datasets and identifying anomalous behavior in real-time, are becoming indispensable. Companies like Darktrace exemplify this trend by utilizing machine learning algorithms to create self-learning security measures that adapt to new attack vectors.
Research indicates that AI-driven security solutions could reduce the time it takes to detect and respond to a breach by over 75%. By leveraging predictive analytics, these tools prepare organizations to combat potential threats proactively rather than merely reacting to them. Furthermore, AI advancements are enabling firms to automate remediation processes, allowing IT teams to focus on strategic initiatives rather than getting bogged down by routine security tasks.
Enhancing Privacy with Decentralized Identity Solutions
The rise of decentralized identity solutions is reshaping user authentication and data privacy. Built on groundbreaking blockchain technology, these solutions grant users more control over their personal data while minimizing exposure risks typically associated with centralized systems. Projects like Sovrin are pioneering efforts in this field, striving to create self-sovereign identities that enhance trust and transparency.
In a landscape where identity theft remains a significant concern, particularly for organizations working with sensitive customer data, decentralized solutions present a viable alternative. By allowing users to manage their identities independently of third-party services, the vulnerabilities linked to traditional databases are effectively diminished. Moreover, this model supports regulations like the General Data Protection Regulation (GDPR), which emphasize user consent and data protection.
- Improvised Data Handling: Organizations can ensure that user data is securely stored and accessed only by authorized users.
- Reduced Risk of Breaches: The decentralized approach lessens the chance of large-scale data breaches, as there is no single point of failure.
- Enhanced User Privacy: Users have the autonomy to share their information selectively, retaining more control over their personal details.
As we move deeper into 2024, embracing these emerging trends in data security is no longer a choice, but a necessity. By integrating dynamic models like Zero Trust, leveraging the capabilities of AI, and transitioning towards decentralized identity frameworks, organizations can significantly enhance their security posture and protect their valuable data assets more effectively.
| Category | Details |
|---|---|
| Zero Trust Security | This approach assumes that threats could be internal or external, demanding strict identity verification for every user. |
| AI-Driven Security Analytics | Utilizing machine learning algorithms to predict and respond to security breaches preemptively. |
| Data Encryption Upgrades | Next-generation encryption technologies will enhance the security of data at rest and in transit. |
| Automated Compliance Monitoring | Automated systems ensure adherence to data protection regulations, minimizing risks and lowering overhead costs. |
In 2024, these emerging trends will play a vital role in shaping a robust landscape for data security in the cloud. Organizations adopting these methodologies will not only enhance their defense strategies but also cultivate a culture of continuous improvement in their cloud data protection practices. Leveraging advanced tools, cloud security will become increasingly adaptive and resilient to evolving threats. Stakeholders interested in data security must pay close attention to these trends, as they herald a new era of innovation, compliance, and risk management in cloud solutions.
DISCOVER MORE: Click here for expert tips
Container Security: The New Frontier
As organizations increasingly adopt containerization for their application development and deployment processes, the need for robust container security in cloud solutions has become paramount. Containers, which encapsulate applications and their dependencies, offer significant advantages in terms of scalability and efficiency. However, their inherent complexity also introduces new security challenges that must be addressed as we navigate through 2024.
The rise of container orchestration platforms like Kubernetes has revolutionized how applications are managed but has simultaneously created vulnerabilities that cybercriminals are eager to exploit. According to recent studies, over 50% of organizations leveraging containers have reported security incidents tied directly to misconfigurations or vulnerabilities in their container environments. This alarming statistic underscores the importance of proactive measures in secure container deployments.
To combat these risks, organizations are increasingly turning to cloud-native security solutions designed specifically for container security. These solutions provide tools for continuous vulnerability scanning, runtime protection, and compliance monitoring, ensuring that any vulnerabilities are identified and mitigated before they can be exploited. Industry leaders like Aqua Security and Twistlock are at the forefront of this trend, offering specialized platforms that integrate seamlessly into existing development workflows to enhance security without sacrificing agility.
The Role of Encryption in Data Protection
With cyberattacks on the rise, the importance of data encryption cannot be overstated. In 2024, there is a renewed focus on end-to-end encryption as a standard practice for protecting sensitive data in transit and at rest within cloud environments. Recent surveys indicate that nearly 60% of organizations prioritize encryption strategies as a primary line of defense against data breaches.
Innovations in encryption technologies, such as homomorphic encryption, are gaining traction, allowing companies to perform computations on encrypted data without needing to decrypt it first. This revolutionary approach ensures that sensitive information remains secure and private even while being processed. Companies like Microsoft and Google Cloud are already implementing such advanced encryption methods, reinforcing their commitment to data privacy and security.
Furthermore, the use of encryption keys is becoming more sophisticated, with trends leaning towards hardware security modules (HSMs) and key management services (KMSs) that enhance the security of cryptographic keys. By ensuring that encryption keys are stored separately from encrypted data, organizations can significantly reduce the likelihood of unauthorized access or data leakage.
Cloud Security Posture Management (CSPM)
In the ever-evolving landscape of cloud services, adopting a proactive approach to cloud security is critical. This has led to the emergence of Cloud Security Posture Management (CSPM) as a pivotal tool in 2024’s data security arsenal. CSPM solutions continuously monitor cloud environments to identify compliance and security risks, ensuring that configurations adhere to best practices and regulatory requirements.
According to reports, organizations that implement CSPM save an average of 30% on remediation costs thanks to the early detection and correction of vulnerabilities. CSPM tools not only reduce the risk of data breaches but also enhance overall visibility and control over cloud resources. Major players like Palo Alto Networks and Check Point are offering CSPM solutions that empower enterprises to automate compliance checks and remediate vulnerabilities swiftly.
As the cloud continues to be a central part of digital transformation strategies for businesses in the United States, embracing these emerging trends—container security, data encryption advancements, and CSPM—becomes essential for enhancing data protection measures and defending against increasingly sophisticated cyber threats.
DON’T MISS OUT: Click here for essential tips
Conclusion
As we look ahead to 2024, the landscape of data security for cloud solutions is evolving at an unprecedented pace, necessitated by the rise in sophisticated cyber threats and the growing reliance on cloud technologies. Organizations must remain vigilant and adaptive to these challenges by integrating emerging trends such as container security, advanced data encryption, and Cloud Security Posture Management (CSPM). By doing so, they position themselves to not only safeguard sensitive information but also to cultivate a robust security posture that enhances trust in their digital operations.
The focus on container security emphasizes the need for specialized tools that address the unique vulnerabilities within containerized environments. As businesses navigate a more complex application development ecosystem, employing dedicated security measures will be critical to preventing breaches linked to misconfigurations and vulnerabilities.
Data encryption also plays a pivotal role, especially with advancements such as homomorphic encryption paving the way for more secure data processing without compromising privacy. By prioritizing encryption strategies, organizations can fortify their defenses against data breaches, ensuring compliance with increasingly stringent regulations.
Finally, the proactive approach of CSPM offers a game-changing advantage, enabling organizations to identify and mitigate vulnerabilities in real-time. Investing in these cutting-edge solutions equips enterprises with the agility needed to respond promptly to emerging threats while optimizing their cloud security posture.
In a world where data is often considered the new oil, harnessing these trends will be crucial as organizations strive to protect their valuable assets in 2024 and beyond. Thus, stakeholders must stay informed and innovative, continuously seeking new strategies that will not only protect against current threats but also anticipate future challenges in the fast-paced realm of cloud security.
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.